Method to Bypass ChatGPT VPN Detection
Categories:
How to handle ChatGPT errors
“Unable to load site”
“Please try again later, if you are using a VPN, try turning it off.”
“Check the status page for information on outages.”
Foreword
ChatGPT is still the chatbot with the best user experience, but when using it in China, due to network environment restrictions, we need to use a VPN to access ChatGPT. However, ChatGPT’s detection of VPNs is quite strict; if it detects a VPN is in use, it will directly deny access. This article introduces a method to bypass ChatGPT’s VPN detection.
Others have mentioned changing IPs to bypass the block, but the region of the IP we generally use is already one that can provide service, so this method may not be the actual reason for the denial of service.
Some people also mention that VPNs with a large number of users are easily identified, persuading others to buy more expensive VPNs with fewer users. This is also unlikely to be a reasonable reason. In today’s world of IPv4 scarcity, even overseas, there are many communities using NAT to allocate ports, sharing a single IPv4 address. If ChatGPT were to block one, it would block a large group. As a widely used service, such a detection design is definitely unreasonable.
For a public service, detecting source IP consistency is more reasonable. The characteristic of paid VPNs is usually that they limit traffic or speed, so most users who use VPNs choose to bypass them according to rules. They bypass addresses that can be accessed directly through their own ISP to reduce traffic consumption or get faster access speeds, only importing traffic to the proxy when accessing addresses blocked by the firewall. This different way of accessing the target service can cause source address inconsistency. For example, accessing service A requires communication with both domain X and domain Y, but the firewall only intercepts domain X. Then, for the same request from service A, the source IPs of different stages of access are seen as inconsistent.
Solving the source IP inconsistency issue caused by proxy policies can bypass ChatGPT’s VPN detection.
VPN rules usually contain domain rules, IP rules, etc.
We also need to know that the IP result of domain resolution can vary by region. For example, when I am in region A, it resolves to a nearby service IP, and when I am in region B, it resolves to a different IP. Therefore, the choice of DNS is also very important.
DNS Selection
There are many DNS protocols now, and UDP:53 is a very outdated and extremely insecure protocol. China has even included DNS services as a primary item in enterprise operations. This mainly stems from the fact that in the past few decades, various ISPs in China have used DNS hijacking and HTTP to insert a large number of redirect ads, deceiving many network novices and attracting numerous complaints. Although Chrome/Edge now automatically redirects to HTTPS and marks HTTP sites as insecure, there are still many small community-level network service providers in China, as well as various modified versions of Chromium with old versions, so DNS hijacking and HTTP hijacking still exist.
Therefore, we need to choose a secure DNS service protocol to avoid DNS hijacking. Based on personal experience, Alibaba Cloud’s 223.5.5.5 is good enough. Of course, when I mention 223.5.5.5, I definitely don’t mean the alidns over UDP:53, but the DoH or DoT protocol. When configuring, you need to use tls://223.5.5.5 or https://dns.alidns.com/dns-query in your configuration.
The alidns service is not polluted most of the time, only during a few sensitive periods. You can also use my self-hosted long-term DNS service tls://dns.jqknono.com, with upstreams from 8.8.8.8 and 1.1.1.1, which accelerates access through caching.
Domain Rules
The detection page that is first opened will contain the detection logic, verifying the source IP by sending requests to different domains. Therefore, it is necessary to maintain the consistency of domain proxying.
In addition to its own domain openai, the domains accessed by the ChatGPT webpage also include third-party domains like auth0 and cloudflare.
You can manually write the following rules:
# openai
- DOMAIN-SUFFIX,chatgpt.com,PROXY
- DOMAIN-SUFFIX,openai.com,PROXY
- DOMAIN-SUFFIX,openai.org,PROXY
- DOMAIN-SUFFIX,auth0.com,PROXY
- DOMAIN-SUFFIX,cloudflare.com,PROXY
How to Test Domain Rules
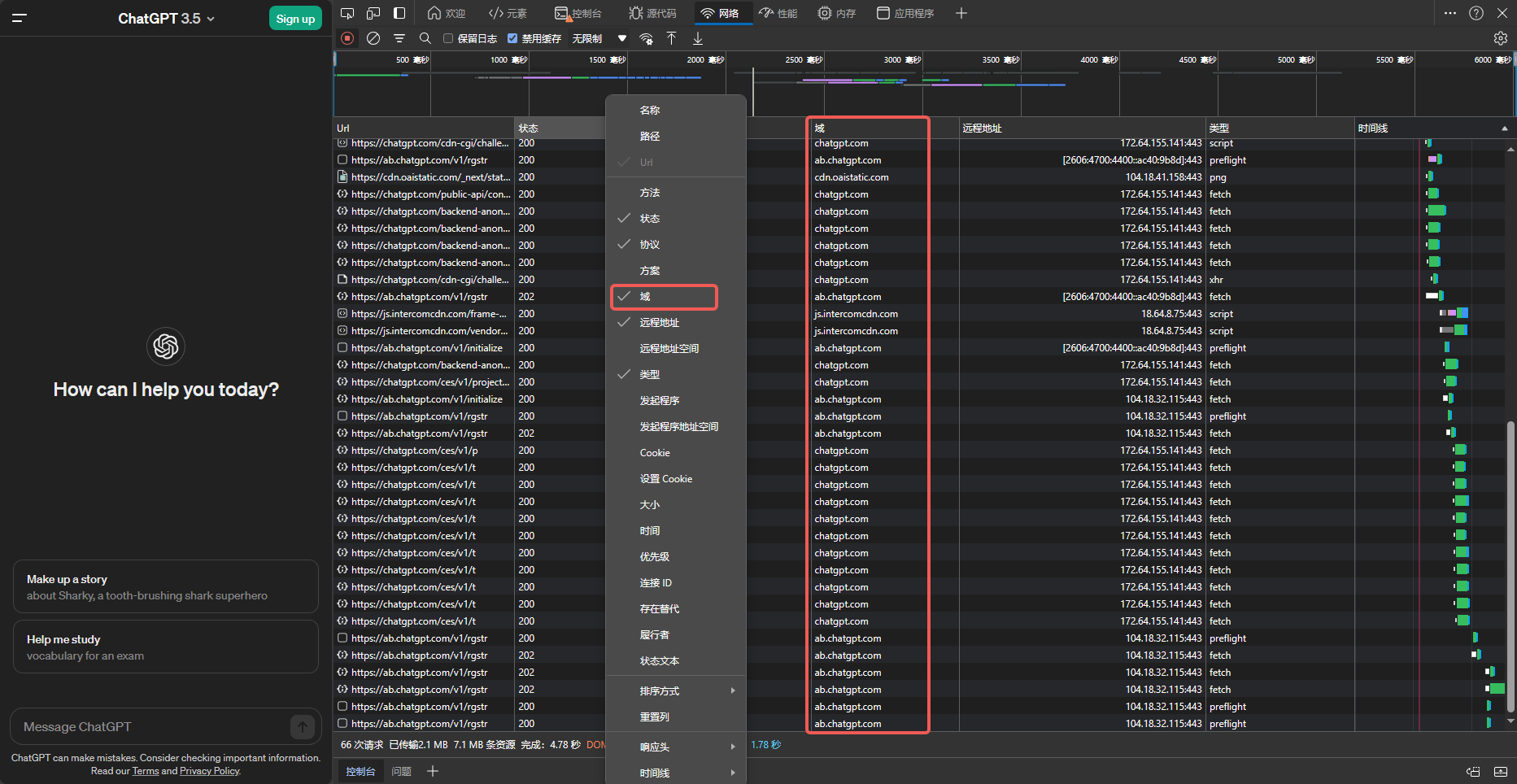
The domains listed above may change as ChatGPT’s business develops. Here is how to obtain the domains.
- Open an InPrivate window in your browser. A private window can avoid the influence of cache/cookies, etc.
- Press
F12to open the console and select theNetworktab. - Visit
chat.openai.comorchatgpt.com. - The image below shows the domains used by ChatGPT at the time this article was written.
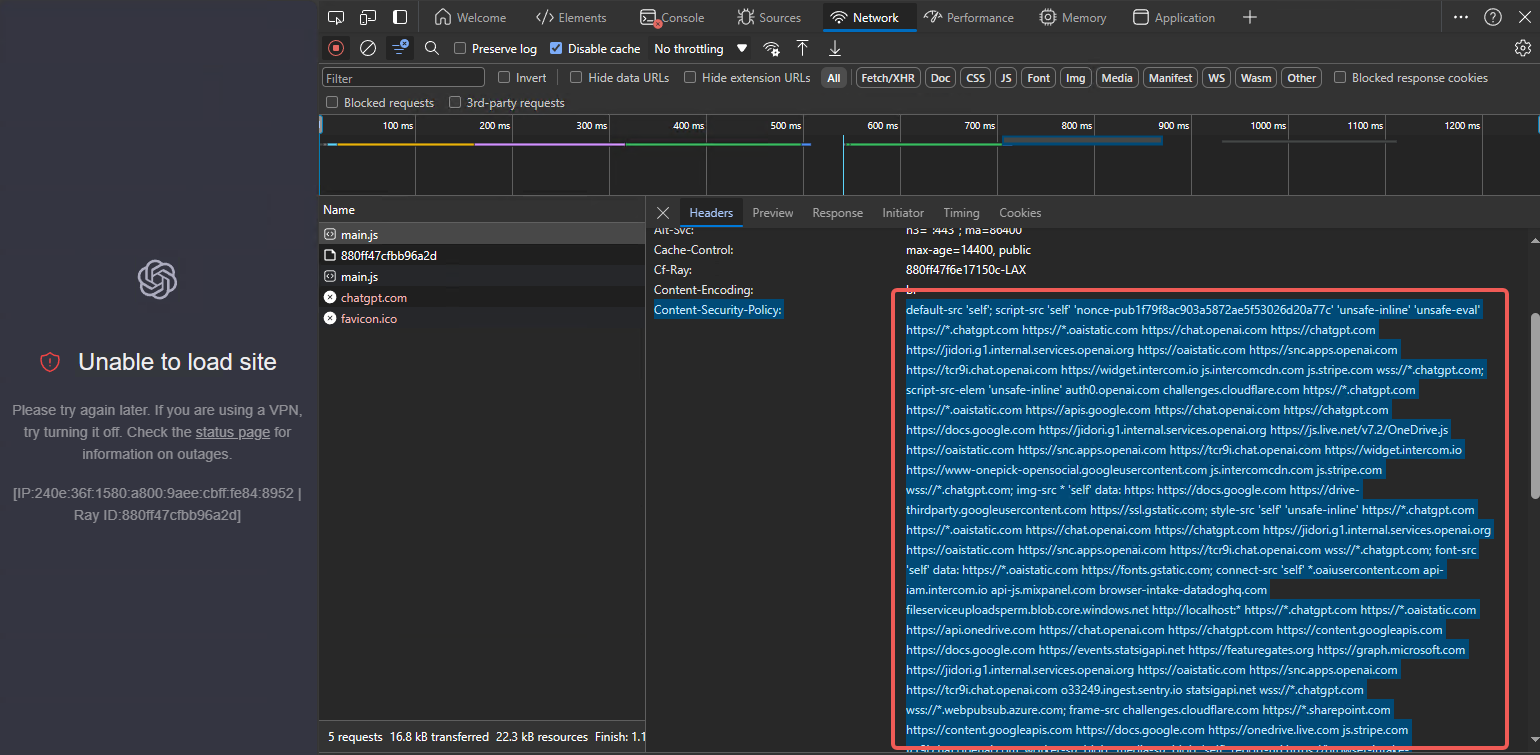
Adding only these few domains may still not be enough. Here, we analyze the specific details of the failed connections. The Content-Security-Policy of the challenge request contains many domains. We need to add them one by one to the proxy policy.
# openai
- DOMAIN-SUFFIX,chatgpt.com,PROXY
- DOMAIN-SUFFIX,openai.com,PROXY
- DOMAIN-SUFFIX,openai.org,PROXY
- DOMAIN-SUFFIX,auth0.com,PROXY
- DOMAIN-SUFFIX,cloudflare.com,PROXY
# additional
- DOMAIN-SUFFIX,oaistatic.com,PROXY
- DOMAIN-SUFFIX,oaiusercontent.com,PROXY
- DOMAIN-SUFFIX,intercomcdn.com,PROXY
- DOMAIN-SUFFIX,intercom.io,PROXY
- DOMAIN-SUFFIX,mixpanel.com,PROXY
- DOMAIN-SUFFIX,statsigapi.net,PROXY
- DOMAIN-SUFFIX,featuregates.org,PROXY
- DOMAIN-SUFFIX,stripe.com,PROXY
- DOMAIN-SUFFIX,browser-intake-datadoghq.com,PROXY
- DOMAIN-SUFFIX,sentry.io,PROXY
- DOMAIN-SUFFIX,live.net,PROXY
- DOMAIN-SUFFIX,live.com,PROXY
- DOMAIN-SUFFIX,windows.net,PROXY
- DOMAIN-SUFFIX,onedrive.com,PROXY
- DOMAIN-SUFFIX,microsoft.com,PROXY
- DOMAIN-SUFFIX,azure.com,PROXY
- DOMAIN-SUFFIX,sharepoint.com,PROXY
- DOMAIN-SUFFIX,gstatic.com,PROXY
- DOMAIN-SUFFIX,google.com,PROXY
- DOMAIN-SUFFIX,googleapis.com,PROXY
- DOMAIN-SUFFIX,googleusercontent.com,PROXY
IP Rules
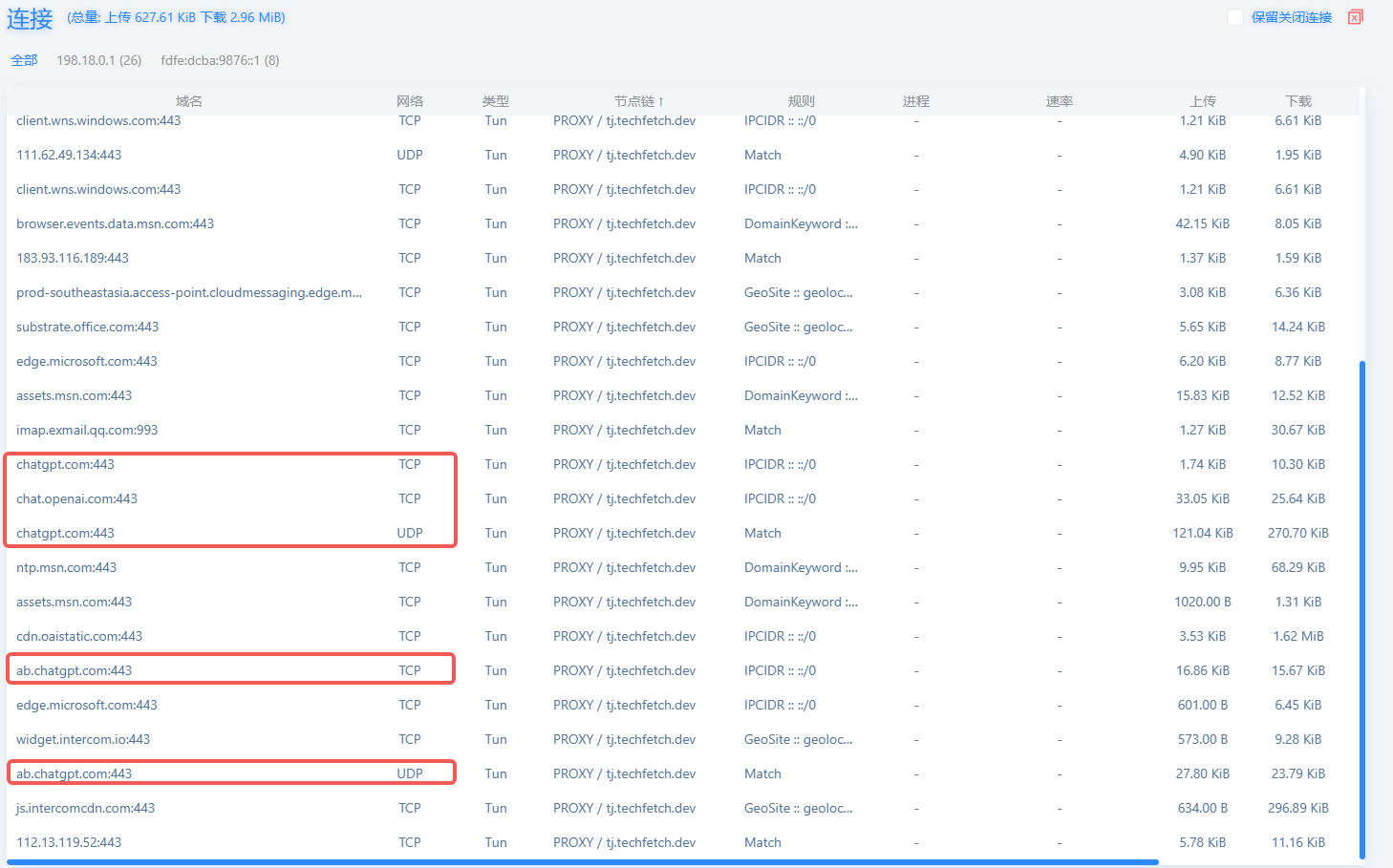
If you still cannot access chatgpt.com after trying the steps above, there may still be IP-based detection behavior. Here are some IPs I found through connection tracking. You can try them yourself. It should be noted that these IPs may not be applicable to every region, and you may need to try them yourself.
# openai
- IP-CIDR6,2606:4700:4400::6812:231c/96,PROXY
- IP-CIDR,17.253.84.253/24,PROXY
- IP-CIDR,172.64.152.228/24,PROXY
- IP-CIDR,104.18.35.28/16,PROXY
How to Test IP Rules
You need to understand your VPN client tool. On the connection tracking display page, observe the new connections and try adding rules based on the IP addresses of these connections.
Here is a simple description of the steps:
- Open an InPrivate window in your browser. A private window can avoid the influence of cache/cookies, etc.
- Visit
chat.openai.comorchatgpt.com. - Observe new connections in your VPN client and add these connections to the proxy rules.
Protocol Rules
QUIC is an encrypted protocol based on UDP. ChatGPT makes extensive use of QUIC traffic, so the VPN’s server and client need to support UDP proxying. Many VPNs do not support UDP, which is one of the reasons why ChatGPT cannot be accessed. Both the client and server must support UDP, and the user must also configure it explicitly. Some clients are configured not to proxy UDP traffic by default. If you are not familiar with UDP settings, you can set your client to block QUIC traffic or disable QUIC in your browser settings. When the browser finds that QUIC is not working, it will automatically switch to HTTP/2 based on TCP. QUIC is an encrypted protocol based on UDP, which can often provide a smoother experience. If you are interested, you can try it yourself.
Simplest Configuration – Whitelist Mode
Configure to direct-connect only for China IPs, and route all unmatched traffic through the proxy. This ensures access to ChatGPT as well as other foreign services.
The disadvantage of this method is high traffic consumption, and the network fluency experience depends on the quality of your VPN. If you are confident in your VPN, you can try this method.
Of course, you still need to remember to enable UDP proxying.