A Vendor's Method to Prevent DNS Blocking
Categories:
Recently, I discovered abnormal access behavior from DNS public service IPs, with dozens of repeated requests per second for the same domain name, completely disregarding DNS protocols and ignoring the global Time-to-Live (TTL) value.
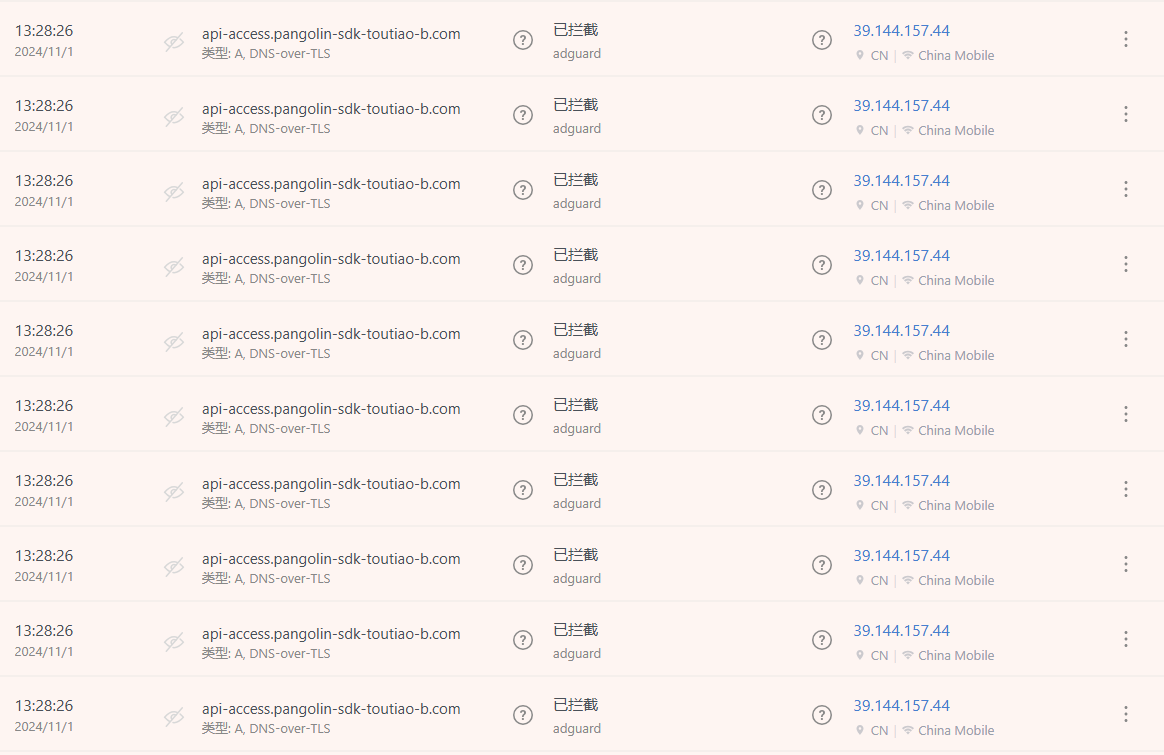
Initially, I thought this IP was an attacker. After observing the traffic, I found that it was primarily a specific vendor’s App making frantic DNS requests. The backend sets TTL=10, meaning the received DNS query response has a lifespan of 10 seconds. During these 10 seconds, the requester should use this response value instead of requesting the DNS server again. However, this App makes dozens of identical requests per second, indicating that it does not properly handle the TTL value according to DNS protocols. In the backend request blocking statistics, over 90% of the requests are for this domain.
It’s possible that this vendor is aware of DNS blocking techniques and has adopted a strategy of “if you don’t allow me access, I’ll have user Apps directly launch DoS attacks on your DNS server.” Since the backend also limits burst requests to only 20 per second, this reckless behavior simultaneously affects users’ other normal DNS queries, impacting the normal operation of other Apps.
When operations staff see such frantic single-IP behavior repeatedly requesting the same domain name, they have no choice but to allow it through, even if they don’t want to.